Documentation Index
Fetch the complete documentation index at: https://jam.dev/docs/llms.txt
Use this file to discover all available pages before exploring further.
Creating a token
Open Settings → MCP
Go to Settings → MCP.
Navigate to Personal Access Tokens
Scroll to the Personal Access Tokens section and click Create token.
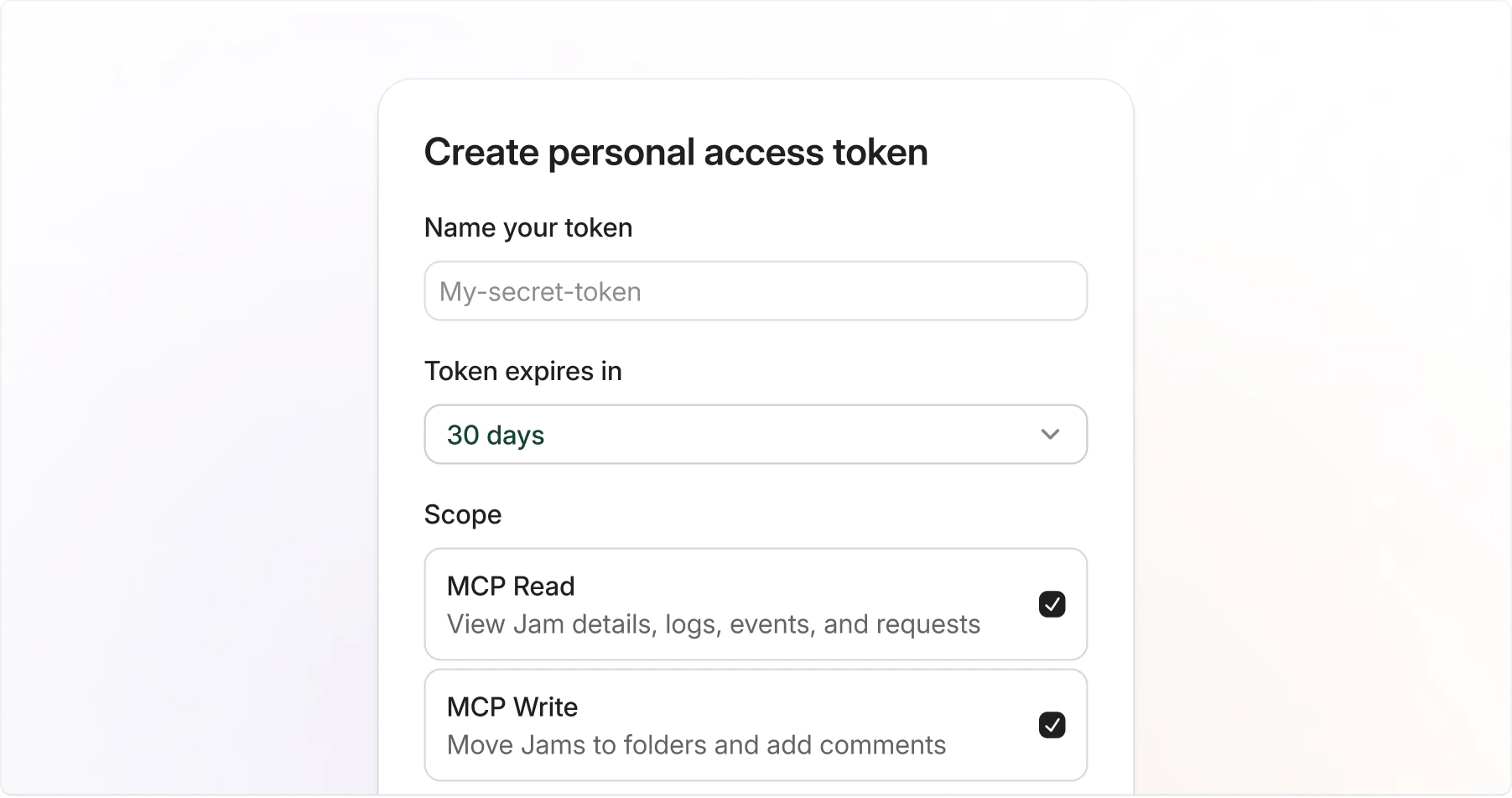
Fill in the token details
Provide the following:
- Name: A label to identify the token, such as “Cursor” or “Claude Code”.
- Expiration: How long the token is valid: 7 days, 30 days, 90 days, or 1 year.
- Scopes: The permissions the token needs. See the Scopes section below.
Token format
Jam PATs follow a recognizable format:jam_pat_ prefix makes it easy to identify Jam tokens in your configuration and helps secret scanners detect accidental exposure.
Using a token with MCP clients
Use your PAT as a Bearer token when configuring your MCP client. Replacejam_pat_... with your actual token.
- Claude Code
- Cursor
- VS Code / Windsurf
Scopes
Scopes control what a token can do. Select only the scopes you need.| Scope | Description |
|---|---|
mcp:read | View Jam details, logs, events, and network requests. |
mcp:write | Move Jams to folders and add comments. |
Managing tokens
Viewing your tokens
Go to Settings → MCP to see all personal access tokens for the current workspace. The list shows each token’s name, scopes, last used date, and expiration status.Revoking a token
Find the token
Go to Settings → MCP and locate the token you want to revoke.
Expiration
All tokens have a mandatory expiration date. Choose the expiration period that matches your use case:| Duration | Recommended for |
|---|---|
| 7 days | Short-lived tasks or testing |
| 30 days | Active development work |
| 90 days | Longer-running integrations |
| 1 year | Stable, long-term integrations |
Security best practices
- Use short-lived tokens: Choose the shortest expiration that works for your use case.
- Limit scopes: Grant the permissions the token needs.
- Never commit tokens: Store tokens in environment variables or your MCP client’s secure credential storage, not in files checked into version control.
- One token per client: Create separate tokens for each MCP client so you can revoke them independently.
- Revoke immediately if compromised: If a token may have been exposed, revoke it right away and create a replacement.
